Have you ever stopped to think about the security of your online activity? With the increasing amount of sensitive information being shared over the internet, ensuring your network is secure is more critical than ever. One of the best ways to do that is by using a Virtual Private Network, or VPN for short.
A VPN creates a private, encrypted connection between your device and the internet. This means that any data being transmitted over the network is kept safe from hackers and cyber threats. It also allows you to browse the web anonymously, preventing anyone from tracking your online activity. Think of it like a secret tunnel that keeps prying eyes and hackers out while you safely surf the web.
But that’s not all a VPN can do. It can also bypass geo-restrictions, giving you access to content that may be blocked in your region. And for businesses, VPNs are essential for securing remote work connections and protecting sensitive company information.
This blog will dive into how VPNs work and the different types available. We’ll also explore how VPNs can improve network security and the factors to consider when choosing a VPN service. So whether you’re a business owner or someone looking to protect your personal information, this is your guide.
How VPN Improves Network Security
One of the biggest advantages of using a VPN is the improved security it provides for your network.
Here are a few key ways how VPNs improve network security:
- Encryption: One of the most important ways VPNs improve security is by encrypting the data transmitted over the network. This means that even if someone tries to intercept your data, they wouldn’t be able to read it without the encryption key.
- Protection Against Hackers: VPNs protect against hackers by creating a secure encrypted tunnel for your data to travel through. This makes it much harder for hackers to access your information and steal sensitive data like login credentials and credit card information.
- Prevention of Unauthorized Access: VPNs prevent unauthorized access to your network by requiring authentication before a connection can be made. This ensures that only authorized users can access your network.
- Ensuring Privacy and Anonymity: VPNs provide privacy and anonymity by masking your IP address and making it much harder for anyone to track your online activity. This is especially important for anyone who lives in countries with strict internet censorship laws.
Different Types of VPN
1. Remote-Access VPN
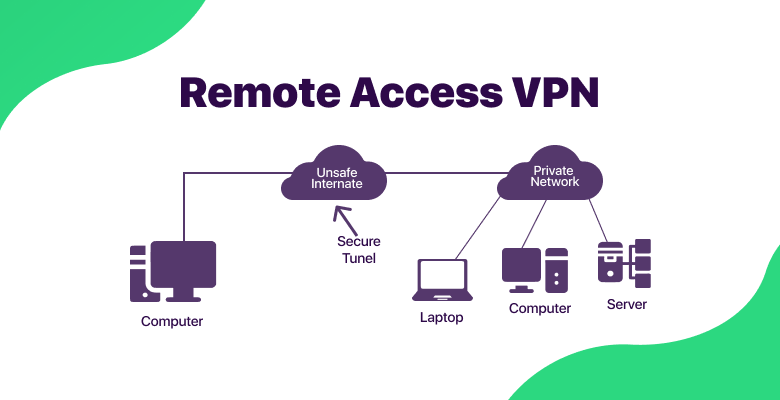
A remote-access VPN, as the name suggests, is a type of VPN that allows remote users to securely access a corporate network. This type of VPN is useful for organizations that have employees working remotely, such as during the COVID-19 pandemic in 2020. With a remote-access VPN, remote workers can connect to the corporate network as if they were physically in the office. This allows them to access important business operations, such as company databases and applications, from anywhere in the world. Remote-access VPNs also provide higher security for remote workers as they keep their data and connections safe from prying eyes. This is especially important for organizations that deal with sensitive information, such as financial institutions and healthcare providers.
2. Site-to-Site VPN
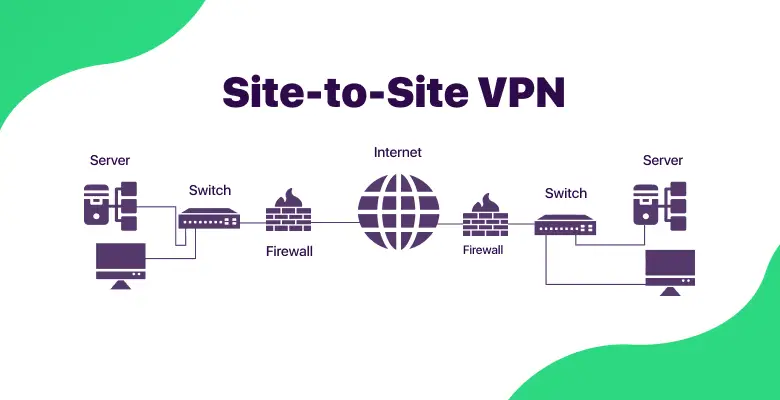
A site-to-site VPN is a type of VPN connection that allows communication between two different networks located in separate geographical locations. This type of VPN connection is typically used to connect a branch office to a main office or connect multiple offices to form a single network. The communication between the two networks is typically encrypted to ensure the security and privacy of data. A site-to-site VPN typically establishes the connection using protocols such as IPsec or SSL. The VPN gateway at each location manages the connection and ensures that the data is properly encrypted and decrypted as it travels between the two networks.
3. VPN-as-a-Service
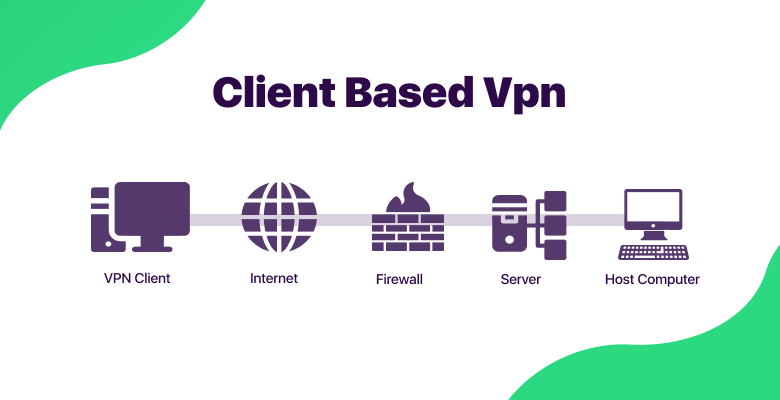
VPN as a Service, also known as a “Cloud VPN”, is a type of VPN hosted in a cloud-based infrastructure. This type of VPN is particularly useful for consumers, as it allows them to protect themselves while connecting to the internet via insecure public Wi-Fi and provides some anonymity while accessing the internet. This allows the user to hide their real IP address and location, making it much harder for anyone to track their online activity. VPN-as-a-service providers typically offer a subscription-based model where the user pays a monthly or annual fee to access the VPN service. This type of VPN is easy to set up and use, and there is no need for the user to have the technical knowledge to configure the VPN.
Also read: Do You Need a VPN at Home?
Use Cases of VPN in Network Security
VPNs have a wide range of use cases in network security. Here are a few examples:
- Businesses and Remote Work: VPNs are useful for businesses that have employees working remotely. With a VPN, remote workers can securely access the corporate network as if they were in the office.
- Public Wi-Fi and Internet Cafes: Public Wi-Fi networks and internet cafes are often unsecured and can be a breeding ground for hackers looking to steal sensitive information. With a VPN, users can encrypt their data and hide their IP address, making it much harder for hackers to access their information.
- Online Shopping and Banking: When shopping online, it is important to keep your personal information and financial data secure. A VPN can encrypt your data and keep your information safe from hackers and other cyber threats, making online shopping and banking safer.
- Accessing Restricted Content: VPNs can also bypass geo-restrictions and access content that may be blocked in a specific region. This can be useful for people traveling abroad or for those who want to access content from a different country.
Choosing a VPN Service
When choosing a VPN service, you need to consider several factors to ensure that you get the best service for your needs.
First, consider the security and encryption protocols offered by the VPN service. Look for a VPN service that uses strong encryption protocols such as OpenVPN or IKEv2 to keep your data safe from hackers and other cyber threats.
Next, consider the number of servers and locations the VPN service offers. A larger number of servers and locations will give you more options for connecting to the internet, allowing you to bypass geo-restrictions and access content that may be blocked in your region.
Third, consider the logging policy of the VPN service. A good VPN service should not keep logs of your online activity, as this can put your privacy at risk.
Finally, consider the cost of the VPN service. While some VPN services may be more expensive than others, they may also offer more features and better security.
When it comes to recommended VPN services, Surfshark is one of the best options available. Surfshark offers a wide range of security and encryption protocols, a large number of servers and locations, a strict no-logs policy, and a very affordable price. You can check out Surfshark at Surfshark.com
Conclusion
In this digital age, where we are more dependent on the internet than ever before, it’s crucial to take steps to protect ourselves from cyber threats.
VPNs provide a wide range of benefits, including encryption of data transmitted over the network, protection against hackers and cyber threats, prevention of unauthorized access to sensitive information, and ensuring privacy and anonymity online.
We have been using a VPN for a long time, and the peace of mind it provides us when using public Wi-Fi or accessing sensitive information is invaluable.
We highly recommend that everyone implement VPN for their personal and professional use to keep their data and online activities secure.
