About three days ago, I was happily playing some multiplayer video games online with friends when an alert beeped on my computer. It had picked up on a malicious program, malware, trying to communicate with a server elsewhere. Well, the first thing I did was check to see if my security system had quarantined the malware – it had, and then I ran a full scan of my computer just to be sure.
It found three more pieces of malware.
Worse, it couldn’t remove them.
One after the other, I manually tracked down and erased the malware, but it became apparent that something already on my computer was putting them there. I quickly cut access to the internet and began doing another full search and looking through my history to try to guess where it had come from.
Three free anti-virus and anti-malware defenders applied, and this piece of malware is still on here somewhere. Every week I pick up the same .exe files appearing on my computer with no idea where it’s coming from. Internet banking? Online shopping? Logging into any of my accounts? Well, I could, but depending on what the malware is actually doing, it’s really not worth the risk. The thing is, it could have come from anywhere, and until it’s gone, there’s so much I can’t risk doing. So are computer viruses and malware still a threat? Yeah, absolutely.
Also read: How to Remove Soap2Day Virus (Windows & macOS)
What are the options?

So, what can we do about this? Well, the first thing you can do is pay for some proper protection. The free protections out there cover a LOT, but every now and then, certain things can and will get through, so they’re not perfect. So you could pay for it, or you could learn how to prevent it from happening in the first place.
The second option, of course, requires a lot more work than just letting stuff run in the background. If you want maximum security, training yourself with a master of cyber security could be the way to go – especially if you want to be proactive about everything – but there are a few things you can do to protect yourself.
- Get a VPN and use it: A good VPN is not just for pretending you’re in another country to get different streaming services; it also shields you in a bunch of other ways. A good VPN encrypts your internet traffic, routing it through a server owned by the VPN company so that nobody can snoop on your data without direct access to your computer.
- Use unique passwords for everything: a random password generator might help here. Like everything, you can get free password generators that will not only create and store your passwords, but paid-for services are generally much more secure and well worth the investment.
- Multiple emails.
- Clear Your Cache: it retains a lot of information, including your personal address and other information; you can see how to do that here.
- Keep backups of essential data offline and off your hard drive. USB sticks and external hard drives are perfect for this job.
- If you keep backups online, consider paying for the service. Most free cloud services are excellent but paid-for services offer recovery and security services.
- Use online security tools such as browser extensions. If you’re unsure if you trust them or if they’re running correctly, try checking out online services like AMTSO.
- Use Multi-Factor security, even when it’s only optional.
Does everything cost money? Absolutely not; you can get many of these services for free. But, do be careful. One of the main things you need to learn is how clickbait and phishing scams work and what dangers they pose.
Clickbait and Phishing

Clickbait is just funny videos and catchy or misleading headlines. It can also comprise links in email, Facebook, messengers, intrusive advertisements, or suspicious download links. You’ve probably experienced this if you’ve ever received a strange message from a close friend with a link in it. The shorthand is, don’t click on anything you don’t trust. Phishing, on the other hand, is usually a website pretending to be another website or company hoping to trick you into giving them your credentials. Many online download pages are actually phishing links that can cause malware to automatically download and infect your device – and that can include websites pretending to offer free services! Be sure to check the URL of any website you visit and try to download from; if something seems off about it, maybe try looking for a different link.
Chances are good that this last one is what happened to me, and the virus is embedded inside a legitimate program I use all the time.
What worked for me?
So what worked for me? Well, first off, scanning the computer with the standard virus and threat protection service available on Windows is what let me detect there was something wrong in the first place. I do a scan before every use of net banking or similar, and it was this that first alerted me to any issues on my PC. Once the scan was complete and the mysterious .exe files quarantined and erased, I waited 30 minutes and scanned the system again. They’d returned, and even tracking them down and deleting them manually didn’t keep them away for long.
Also read: How to Remove Ytmp3.cc Virus
The next thing I tried was Eset, which worked better than the Windows scanner, it picked up four suspicious files instead of three. Better, but had it solved the problem? Well, it looked like it had at first, but a day later, one of those files was back. So it was better, but clearly not enough.
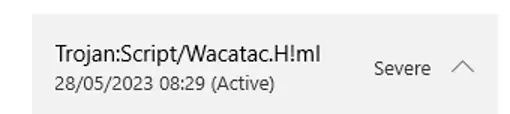
Finally, I tried Hitmanpro – the free version, of course. 76 suspect or infected files later, and I was feeling a lot more confident, but strangely none of them included that Trojan. Was it gone? Well, the regular virus & threat protection had done an excellent job of picking up on this in the past, was it gone?
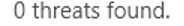
Yes!
I was happy, and a couple of days later, it was still clear. I had my computer back. But even though I managed to fix this with free options, it taught me the value of paying for a high-quality service. Only a combination of luck and persistence kept me protected, but would I be so lucky next time? Probably not. There are a lot of paid-for services I can look into, but if I’ve learned nothing else, it’s that I need to invest in more security than just relying on a few timely scans. The internet is still a dangerous place, and it’s getting sneakier, and if the only way to win is to increase my awareness, knowledge, and real security, then that’s precisely what I’m going to do!
Written By: Louise Jones
