Cybercrime – a Problem of the Present & the Future
It all starts and ends with cybercrime. Without it, companies and individuals would have nothing to defend themselves in cyberspace.
The cybersecurity community and major media companies generally agree on predicting the damage from cybercrime. Thus, cybercrime is one of the most profitable areas in the history of the economy.
The growing wave of cybercrime has led to investment in information security (part of cybersecurity). This does not include the security costs of smart devices, industrial devices, industrial control systems, car safety, and other cybersecurity categories.
Every employee in the field of IT today must also deal with cybersecurity. Everyone from IT and anyone involved in technology must be involved in protecting applications, data, devices, infrastructure, and people.
Also read: Best Browsers for Privacy & Security You Should Try
List of Best Practices for Password Security
1. More Cybersecurity Experts = Better Protection

The shortage of manpower in the field of cybersecurity is more alarming than the numbers indicate. As the world becomes more digital, people are becoming a bigger target for cybercriminals than machines. Cybercrime may become the biggest threat not only to companies but also to individuals, places, and things. We consider cybercrime to be the biggest problem of today’s humanity.
2. Academic Education
There is a significant shortage of computer experts in the world who specialize in computer and network security. For years, we have been hearing about the lack of information technology workforce caused by the expansion of the Internet and the services offered on it, the growing number of users and their electronic devices, as well as the digitalization trend that brings them to the shores of the new digital world.
The industrial revolution has shuffled the maps in the global labor market; some jobs have gone to the archives forever while hundreds of others have appeared on the horizon. Among other things, it has conditioned an extensive range of new jobs in the field of cybersecurity.
3. Non-Formal Education
Is it necessary for future cyber professionals to be masters of informatics, and is academic education a prerequisite for successfully doing this job? For some types of work, the breadth and systematicity built during academic studies is undoubtedly an advantage. In many cases, it is a prerequisite, but for many areas, it is not necessary.
Employers are more likely to seek experience and knowledge of the necessary technologies and the ability to integrate into the company as quickly as possible. The time when trainees were hired and trained for years to take on future functions is behind us, and the time needed to train and introduce new employees is now often equal to the time that a new employee will spend there before new challenges take him to another employer. The lack of staff and the constant outflow of the existing staff can change the practice and behavior of both employers and employees.
Until the state and the economy organize themselves in an age that provides us with continuous learning, when changes in your career and jobs are expected in the fifth decade of your life, when the old diploma loses its luster, consider whether you can see yourself in the boots of people who guard your data and defend your systems daily, often reliving small action movies in just one business day.
4. Better Passwords
In many cases, the password is the only thing that stands between our data and someone’s curious eyes. Passwords are often the weakest link in data protection, and malicious intruders are aware of it. With the growth within the number of employees functioning from home, it’s more important than ever to require care of knowledge security and passwords that protect them. It might be desirable to get rid of passwords from the verification process wherever possible and use two-step authorization or biometric methods. In any case, since passwords are still widely used, it’s the proper time to remind ourselves of the key things for cybersecurity, i.e., the safety of our data and devices.
5. Cyber Hygiene
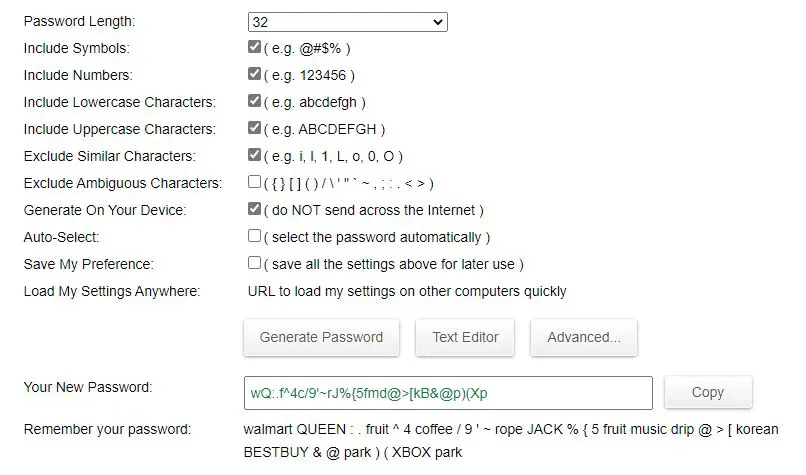
As numerous data leaks shows, weak passwords are the quantity one culprit for security breaches. Not surprisingly, the utilization of common words and plain strings of numbers results in relatively easy guessing of the user password and data theft. For the passwords to be as strong as possible, it’s recommended that they be as long as possible. The longer the password, the harder it’s to guess.
If the password is long, it’ll be harder to guess whether or not it’s composed of straightforward words and/or numbers. It’s easier to crack a brief password, irrespective of the very fact that it’s composed of random letters, numbers, and symbols and is seemingly complicated. An extended password requires longer and more resources to be cracked. The typical hacker usually follows the road of travel and cannot waste an excessive amount of time on an advanced password.
6. Don’t Use One Password For All of Your Accounts
If the password is long and composed of random uppercase and lowercase letters, numbers, and special symbols, it makes it practically impenetrable. If you utilize the identical password for multiple accounts, regardless of how strong, all accounts with the identical password will potentially be available to anyone who breaks protection on just one of these accounts. Don’t let the convenience of using the identical password everywhere expose you to unnecessary risk.
7. Password Managers Are Here to Help
Use a password manager; we all know that a robust password is one that’s long and composed of random uppercase and lowercase letters, numbers, and special symbols. We’d remember a posh password, but what to try and do once we have lots of such passwords?
It’s impossible to recollect such a big amount of complicated passwords, and writing them down on paper or in text files that anyone can see is risky. This is often where applications inherit play that is designed to store our passwords and remember them rather than use – password managers.
They store all the passwords that we enter into them and are protected by one master password or, better yet, another type of authentication. Once you must log in somewhere, your password manager will hump for you. It’s faster, lighter, and safer. These applications have a program that’s very easy and convenient to use. Stay safe; use this app.
8. Don’t Fall For The Bait!
You need to be smart in your weight with what you click to ensure your internet life. Clickbait isn’t just about videos about compiling cats and catchy headlines. It can also contain links in email, messaging apps, and Facebook. “Fishing” links are disguised as secure websites hoping that they will trick you into giving them your information. Launch pages can cause malware to automatically download and infect your device, which automatically compromises your security.
Do not click links in emails or text messages unless they come from a source you are sure of. Even then, be careful; your trusted source may be compromised, or the message may be fake. The same goes for links on social media sites, even in posts that appear to be from your friends. If your post doesn’t seem to fit your friend’s style on social media, it could be hacking.
9. Protect Your Personal Data on Social Networks
Data on social networks is not secure. You can download your data to see what all social media knows about you. It may open your eyes, especially if you are a person who routinely clicks on quizzes that require access to your social media account. You don’t need to know which space hero or villain you are.
You can drastically reduce the amount of data that goes to social networks by completely disabling the sharing platform. Once you do, your friends will no longer be able to disclose your personal information. You can’t lose data from apps because you can’t use them. And you can’t use social networks to sign in to other sites (which has always been a bad idea).
10. Don’t Make Your Posts Public
Of course, other social networking sites also need attention. Google probably knows more about you on social media, so take steps to manage Google’s privacy as well. Be sure to configure each location on social media so that your posts are not public. Please think carefully before posting too much in the post, because your friends could share it with others. You can carefully maintain privacy without losing the fun and social media connections.
11. Separate Your Work Email From Your Private Email
People who are both well organized and systematic in terms of their security often use separate email addresses for different purposes to keep the network identity associated with them separately. If a phishing email claims that it came from your bank to an account that you only use for social media, you will know that it is fake.
Many pages equate your email address with your username, but some allow you to choose your username. Think about using a different username every time; your password manager remembers it! Now anyone trying to log in to your account must guess both a username and a password.
Frequently Asked Questions (FAQs)
What is the Most Secure Way to Keep Passwords?
There are several password managers that you can use to protect your passwords, like LastPass, iCloud Keychain, 1Password, etc. If you are deep into the Apple Ecosystem, we will recommend you to use the iCloud Keychain. Otherwise, if you are looking for a free password manager, LastPass is your best bet, and otherwise, for subscription-based service, 1Password is the way to go.
Should I Write Down My Password?
If you are looking for top-notch security, we will highly recommend you not to write down your passwords anywhere. If you have a hard time remembering them, we will advise you to use a password manager so that you will only have to remember a single master password.
